How I accidentally found PII documents of almost everyone in Kerala
Sometimes, the most significant vulnerabilities aren't found through sophisticated tools or planned audits—they reveal themselves during casual exploration. This is the story of how a simple curiosity-driven URL tweak led me to uncover a critical Insecure Direct Object Reference (IDOR) vulnerability back in 2021 on a Kerala Government web application, which exposed PII documents of all users. What started as an innocent observation quickly turned into a discovery that exposed private user data and highlighted a serious oversight in access control.
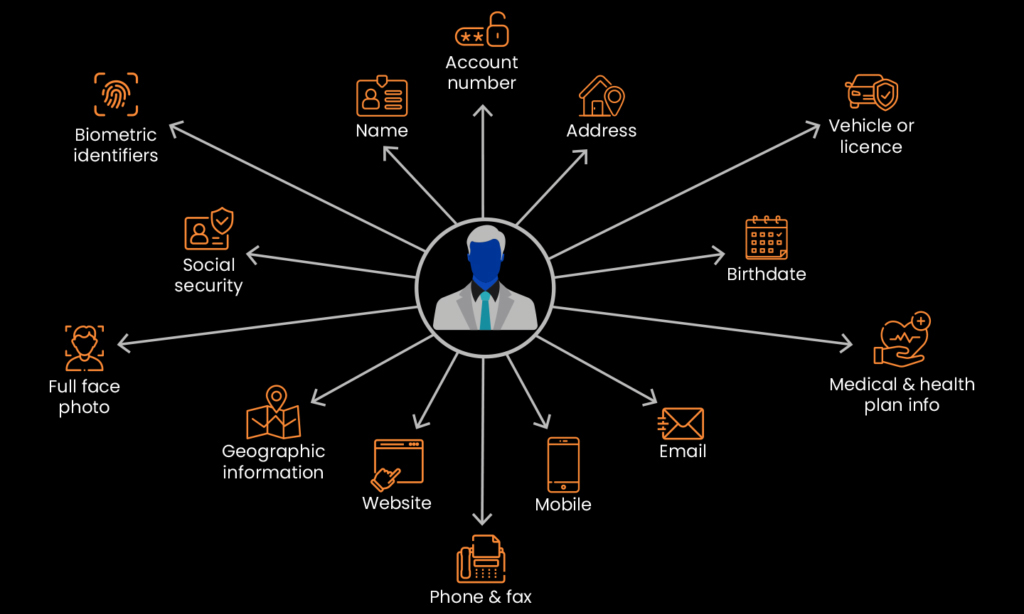
What is PII Leakage?
Personally identifiable information (PII) is any data that could potentially identify a specific individual, such as username,userID or any other personal information. PII Leakage is the exposure of such data.
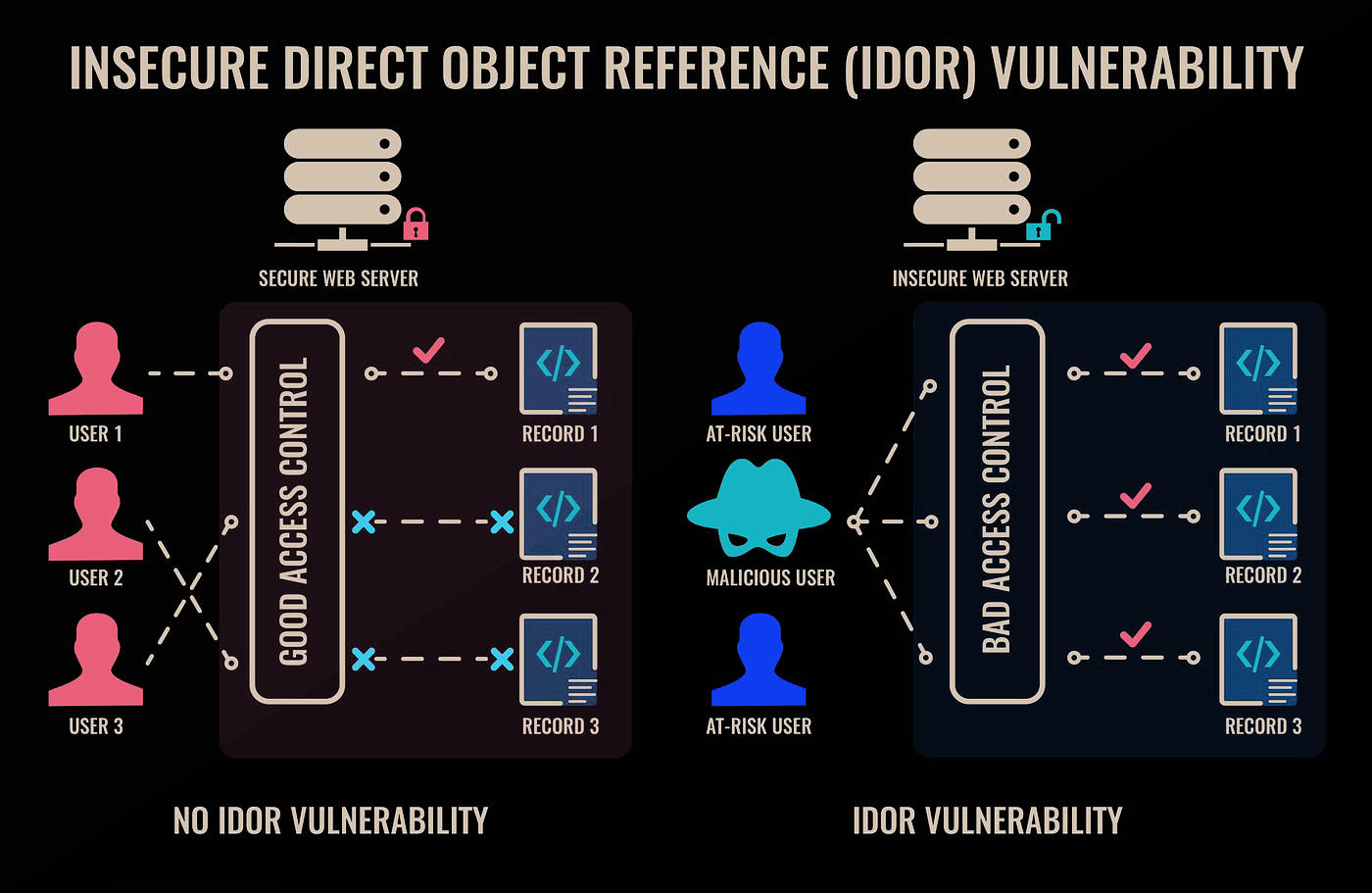
What is IDOR ?
IDOR (Insecure Direct Object Reference) is a security vulnerability that occurs when an application allows direct access to objects (e.g., database records, files, or user accounts) without properly verifying if the user has the necessary permissions. This flaw allows attackers to manipulate input parameters (e.g., object IDs in URLs or API endpoints) to gain unauthorized access to data or perform unintended actions.
Discovery
I was in the process of applying for a certificate on behalf of my younger brother through a prominent Kerala government web application portal, which shall henceforth be referred to as vulnerable-webapp.kerala.gov.in.The platform features a document upload interface, where users are required to submit supporting documents to validate the certificate application. Upon uploading the necessary files, the system provides an option to preview the documents prior to final submission. The URL was like:-
https://vulnerable-webapp.kerala.gov.in/viewImage.do?attachDocsRegNo=XXXXXXX64&hdregId=34735280&token=XXXXXXXX194204031791948604170058
Upon examining the URL, I instinctively recognized its potential. Driven by an insatiable curiosity, my hands acted almost independently, opening the link in a new tab without hesitation.
Assessment
As a penetration tester, I swiftly identified the potential for an Insecure Direct Object Reference (IDOR) vulnerability. Guided by this insight, I proceeded to manipulate the attachDocsRegNo parameter, specifically modifying its final digit to X63, in an attempt to uncover unauthorized access or unintended behavior.
https://vulnerable-webapp.kerala.gov.in/viewImage.do?attachDocsRegNo=XXXXXXX63&hdregId=34735280&token=XXXXXXXX194204031791948604170058
However, a protective mechanism was in place, effectively blocking my access. Undeterred, I realized I would need to devise a strategy to bypass this restriction.
Evading the Security System
To bypass the security measures, the fundamental approach involves understanding how they operate. Upon examining the URL, we notice a token parameter with a long numerical value. This likely serves as a token that verifies whether the user has the necessary permissions to access the specific document. If this assumption holds, the token value would only grant access to the document I previously uploaded, as it is tied solely to that document. Therefore, a straightforward method would be to eliminate this protection mechanism. Additionally, there is another parameter named hdregId, which may represent an identifier associated with the document I uploaded. In summary, to access a document, one must possess the corresponding hdregId and token.
If the application utilizes these two parameters as it's access control mechanism, I needed to investigate what would occur if I removed both the token and hdregID parameters from the URL and attempted to access the document using only the attachDocsRegNo. Consequently, I removed these two parameters from the URL and accessed the document using just the attachDocsRegNo.
https://vulnerable-webapp.kerala.gov.in/viewImage.do?attachDocsRegNo=XXXXXXX63
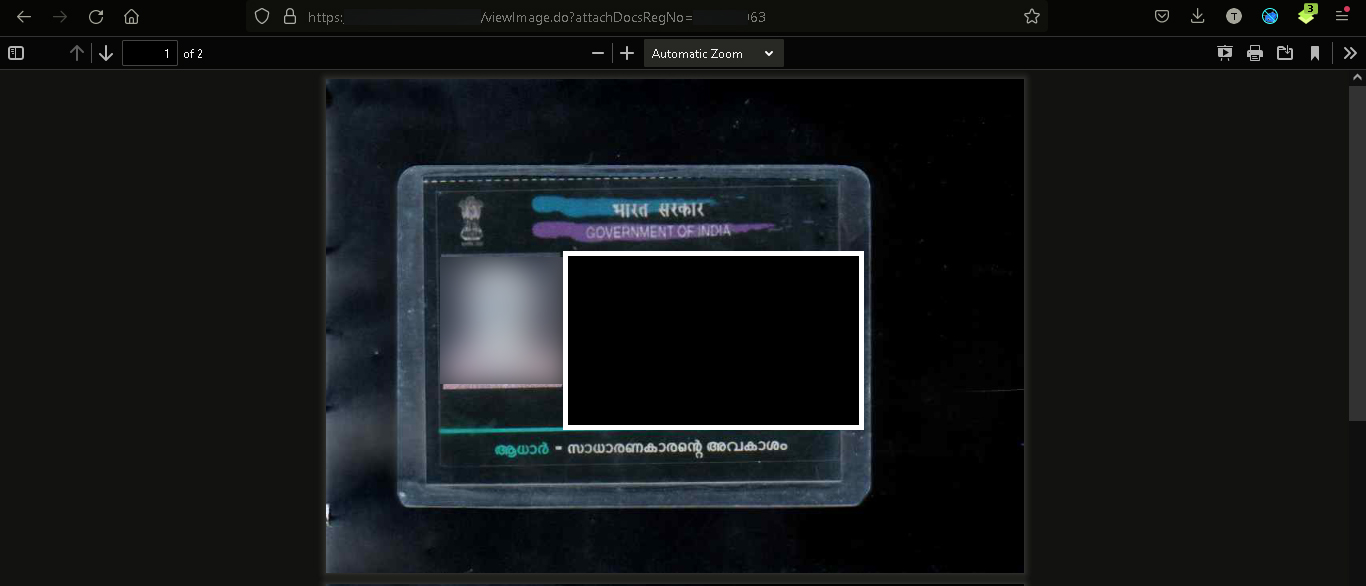
Success!! My calculations proved accurate . I was able to access a specific document belonging to another user by removing these two parameters from the URL. Now, I can simply alter the digits and gain access to any document uploaded into the application. That Includes Pan Cards, Bank Passbooks, Adhaar Cards, Driving License, Ration Cards, ID Cards, etc. I could even access the documents that I have uploaded without any authentication required.
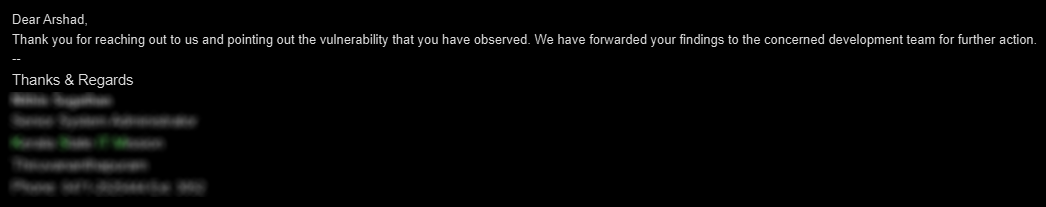
I promptly reported the vulnerability to the web application administrator and the cyber cell, as it exposed the Personally Identifiable Information (PII) of nearly every individual in Kerala. The following day, I received a response email expressing gratitude and assuring me that the vulnerability would be addressed as soon as possible. True to their word, the issue was resolved within a week.
That's how I inadvertently discovered a significant data exposure vulnerability and contributed to its resolution. I hope you found this write-up insightful, and I’d appreciate your feedback through any of the mentioned contact channels.
Happy Hacking...